The Great Seal Legacy: How Medieval Britain Pioneered Modern Authentication Architecture

The Original Certificate Authority
In 1066, when William the Conqueror established the Great Seal of England, he unknowingly created the world's first centralised certificate authority. This wax impression, bearing the monarch's image and Latin inscription, served as the ultimate guarantor of document authenticity throughout the realm. Eight centuries before public key infrastructure emerged, medieval Britain had developed a sophisticated system for establishing trust, preventing forgery, and ensuring document integrity that would be immediately recognisable to any modern cryptographic engineer.
 Photo: William the Conqueror, via images.deepai.org
Photo: William the Conqueror, via images.deepai.org
The Great Seal operated on principles that directly anticipate contemporary digital authentication: a trusted central authority, unique identifiers, tamper-evident packaging, and hierarchical delegation of trust. Understanding this historical precedent not only illuminates the conceptual foundations of modern security architecture but also reveals how British engineers are heirs to an exceptionally mature tradition of authentication design.
Hierarchical Trust Networks
Medieval Britain's seal-based authentication system demonstrated remarkable sophistication in its approach to distributed trust. The Great Seal represented the root certificate authority, but beneath it operated an intricate hierarchy of lesser seals—episcopal seals for church matters, baronial seals for feudal obligations, guild seals for commercial transactions, and personal seals for individual authentication.
This hierarchical structure solved the same fundamental problem that modern PKI addresses: how to establish trust at scale without requiring direct verification by the ultimate authority. A document bearing the seal of the Bishop of Winchester carried authority precisely because the Bishop's own seal had been authenticated by the Crown, creating a chain of trust that enabled secure communication across vast distances.
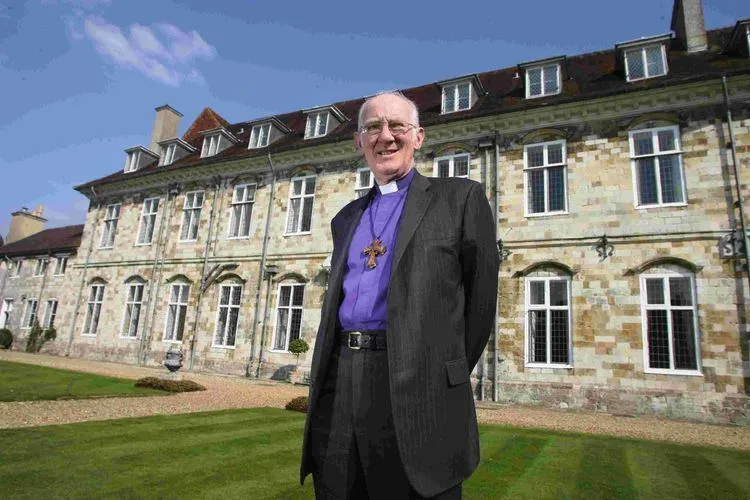 Photo: Bishop of Winchester, via alchetron.com
Photo: Bishop of Winchester, via alchetron.com
Contemporary API authentication systems employ identical principles. When a client application presents a JWT token signed by a trusted identity provider, the receiving service validates the token using public keys that trace back to a root certificate authority—exactly as a medieval clerk might verify a sealed document by confirming the authenticity of the seal through its position in the established hierarchy.
Tamper Evidence and Integrity Protection
The physical properties of medieval wax seals provided sophisticated tamper-evidence mechanisms that anticipate modern cryptographic hash functions. A properly applied seal created a unique impression that could not be removed or transferred without obvious damage. The wax itself often incorporated distinctive materials—particular colours, scents, or embedded objects—that made forgery extremely difficult.
More importantly, the sealing process created what cryptographers would recognise as a collision-resistant hash. Each seal impression was unique to its specific application, incorporating not just the seal matrix itself but also variables like the temperature of the wax, the pressure applied, and the particular characteristics of the document surface. This meant that even if an attacker possessed the seal matrix, they could not create an identical impression on a different document.
Modern digital signatures operate on precisely these principles. A cryptographic hash function creates a unique fingerprint of a document's contents, which is then encrypted using the sender's private key. Any modification to the document produces a different hash, making tampering immediately detectable—exactly as any disturbance to a medieval wax seal would reveal attempted forgery.
Witness Chains and Non-Repudiation
Beyond the seals themselves, medieval British authentication systems incorporated sophisticated witness mechanisms that provided what modern security engineers would recognise as non-repudiation capabilities. Important documents typically required multiple witnesses whose own seals or marks accompanied the principal seal, creating a distributed verification system that made denial of authenticity extremely difficult.
The Chancery Rolls of medieval England demonstrate this principle in action. Royal grants and charters were not only sealed with the Great Seal but also witnessed by specific officials whose presence was recorded in the document itself. This created an audit trail that enabled later verification even if the physical seal was damaged or disputed.
Contemporary blockchain systems employ similar witness mechanisms through distributed consensus. When a transaction is recorded on a blockchain, it requires validation by multiple independent nodes, creating an immutable record that prevents later repudiation. The conceptual similarity to medieval witness requirements is striking: both systems recognise that single-point authentication, however sophisticated, benefits from distributed verification.
Notarial Validation and Trusted Third Parties
Medieval Britain also developed the institution of notarial validation, where trusted officials would attest to the authenticity of documents and the identity of their creators. These notaries operated under strict professional codes and maintained detailed records of their validations, creating what modern engineers would recognise as a comprehensive audit trail.
The notarial system addressed a fundamental challenge in authentication architecture: how to establish initial identity before authentication mechanisms can operate. A notary's validation served as the medieval equivalent of identity proofing—the process by which certificate authorities verify the identity of entities before issuing digital certificates.
Modern certificate authorities employ remarkably similar procedures. Before issuing an SSL certificate for a domain, the CA must verify that the applicant actually controls that domain through various validation methods. Extended Validation certificates require even more rigorous identity proofing, including verification of legal entity status and authorisation—procedures that would be entirely familiar to a medieval notary.
Cryptographic Innovation in Seal Design
The design of medieval seals incorporated several features that anticipate modern cryptographic principles. Many seals included deliberately complex imagery that was difficult to reproduce accurately, serving as an early form of visual cryptography. The combination of text and images, often incorporating multiple languages and symbolic elements, created authentication challenges that required significant expertise to forge successfully.
Some seals incorporated what modern engineers would recognise as steganographic techniques—hidden elements that were not immediately obvious but could be verified by those who knew what to look for. Royal seals might include subtle variations in crown design or specific arrangements of heraldic elements that served as additional authentication factors.
Legacy Systems and Modern Implementation
The conceptual continuity between medieval sealing practices and modern authentication systems suggests practical approaches for contemporary British engineering teams. Understanding the historical precedent can inform better security architecture decisions and help communicate complex cryptographic concepts to non-technical stakeholders.
Root of Trust Principles: Medieval seal hierarchies demonstrate the importance of establishing clear chains of trust with well-defined root authorities. Modern systems benefit from similar clarity in their trust models.
Multi-Factor Authentication: The combination of seals, witnesses, and notarial validation in medieval systems provides a template for robust multi-factor authentication in contemporary applications.
Audit Trail Design: Medieval chancery practices demonstrate the long-term value of comprehensive record-keeping in authentication systems. Modern implementations should prioritise auditability and forensic capability.
The Enduring British Advantage
Britain's eight-century experience with sophisticated authentication systems provides contemporary engineers with an intuitive understanding of trust, authority, and verification that proves invaluable in designing modern security architectures. This historical foundation explains why British institutions often demonstrate particular sophistication in their approach to digital identity and authentication challenges.
The Great Seal tradition reminds us that effective authentication systems require more than technical sophistication—they depend on institutional frameworks, social conventions, and operational practices that build trust over extended periods. As British engineers continue to shape global authentication standards, they draw upon a uniquely rich heritage of security innovation that began long before the first computer was ever conceived.